 Many thanks to SWLing Post contributor, Franco (K4VZ) , who writes:
Many thanks to SWLing Post contributor, Franco (K4VZ) , who writes:
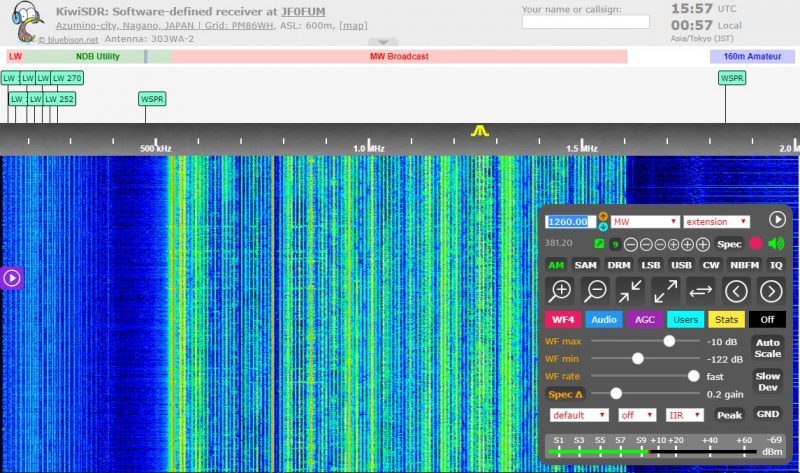
Just a quick note to let you and the SWLing post readers know about the news of a backdoor in the KiwiSDR software that for years “gave root to project developer”.
For years, a backdoor in popular KiwiSDR product gave root to project developer
Users are rattled after learning their devices and networks were exposed.
KiwiSDR is hardware that uses a software-defined radio to monitor transmissions in a local area and stream them over the Internet. A largely hobbyist base of users does all kinds of cool things with the playing-card-sized devices. For instance, a user in Manhattan could connect one to the Internet so that people in Madrid, Spain, or Sydney, Australia, could listen to AM radio broadcasts, CB radio conversations, or even watch lightning storms in Manhattan.
On Wednesday, users learned that for years, their devices had been equipped with a backdoor that allowed the KiwiSDR creator—and possibly others—to log in to the devices with administrative system rights. The remote admin could then make configuration changes and access data not just for the KiwiSDR but in many cases to the Raspberry Pi, BeagleBone Black, or other computing devices the SDR hardware is connected to.
A big trust problem
Signs of the backdoor in the KiwiSDR date back to at least 2017. The backdoor was recently removed with no mention of the removal under unclear circumstances. But despite the removal, users remain rattled since the devices run as root on whatever computing device they’re connected to and can often access other devices on the same network.
“It’s a big trust problem,” a user with the handle xssfox told me. “I was completely unaware that there was a backdoor, and it’s hugely disappointing to see the developer adding backdoors in and actively using them without consent.” [Click here to continue reading the full article…]
Thank you for sharing this, Franco (and many other readers who’ve recently shared this article.
I’ve always been a big fan of the KiwiSDR network and the receiver so, of course, this is disappointing news. It sounds as if there’s no evidence the developer did anything nefarious through this root access backdoor, but they were also well aware it existed. That is, without question, a huge security issue.
The KiwiSDR developer comments here on the SWLing Post so my hope is that, perhaps, they can shed some light on this story in our comments section.